Millions of fingerprints leaked in latest high-profile data breach
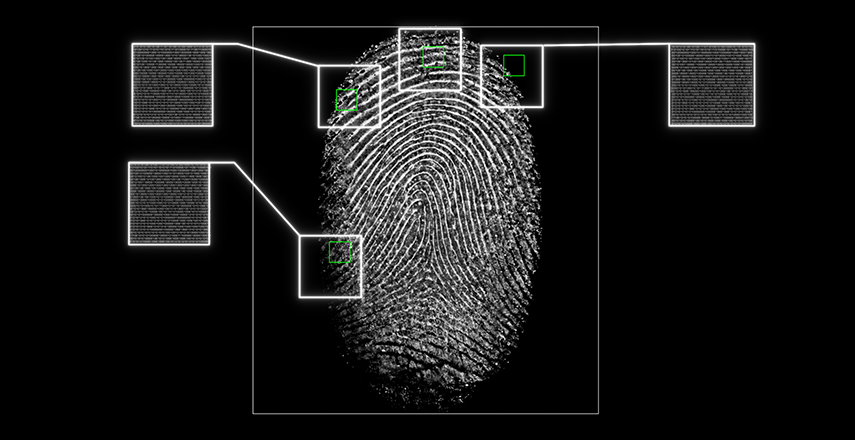
A “huge data breach” in security platform BioStar 2 has been uncovered, revealing the personal information of millions
Researchers at vpnMentor, a blog covering web privacy, recently discovered the data breach, which compromised the private information of millions of people.
Headed by “ethical hackers” Noam Rotem and Ran Locar, the team discovered that “huge parts of BioStar 2’s database are unprotected and mostly unencrypted.”
Over one million fingerprint records and facial recognition biometrics were among the leaked data. Perhaps even more worrying is that these records were tied to personal details, usernames and passwords.
Suprema, the company responsible for the biometric data platform BioStar 2, is one of the world’s top 50 security manufacturers.
vpnMentor was able to access almost 30 million records. These records included fingerprint data, unencrypted usernames and passwords, employee home addresses and personal emails, employee security access clearances, facial recognition information and even images of users.
The BioStar 2 platform is in use worldwide, with over 1.5 million installations. vpnMentor state that the total number of people affected by the breach could be in “the tens of millions.”

The leak raises numerous concerns for the potential of fraud and identity theft, through phishing and direct targeting. Employees could be the targets of blackmail and extortion based on their security clearances, with their personal information used as leverage.
This is the latest in a string of high-profile data breaches. Just last month, American credit card provider Capital One fell victim to a breach. The hacker was able to access the social security numbers and personal information of 100 million Americans.
Two days after discovering the BioStar 2 breach, the researchers who uncovered the hack decided to contact the company’s offices by phone but were largely unsuccessful. Some agents simply hung up on them.
In the blogpost, vpnMentor stated that, upon approaching Biostar 2 to make them aware of the breach, they found them “generally very uncooperative,” adding that their team made “numerous attempts to contact the company over email, to no avail.”
It was only 5 days later that the company responsible took action and closed the breach.