iMazing iPhone backup vs Pegasus spyware infection

Top Business Tech takes a closer look at the iMazing iPhone backup and management app, which can scan for Pegasus spyware.
After discovering private-owned spyware infection, Pegasus, on iPhones, several companies have started developing software to trace the spyware. One company to roll out a service to detect the infection is iPhone backup and management app, iMazing.
What is Pegasus?
Apple devices have been celebrated as “unhackable” or deemed completely safe instead of its competitor Android. Unfortunately, this belief has been proven wrong as politically motivated state-sponsored hacks have risen drastically in recent months.
Pegasus is a zero-click spyware attack sent by iMessage that can collect emails, call records, social media posts, user passwords, contact lists, pictures, videos, sound recordings and browsing histories. It can also access cameras, microphones, listen to calls, and track the phone user’s movements.
Israeli Surveillance company NSO Group used the malware to target over 50,000 individuals. Pegasus is effective against the latest Apple devices and iOS updates and is nearly undetectable by iPhone users as Apple products operate on a closed platform.
Ivan Krsti, head of Apple Security Engineering and Architecture, defended his company’s security efforts. “Apple unequivocally condemns cyberattacks against journalists, human rights activists, and others seeking to make the world a better place. For over a decade, Apple has led the industry in security innovation and, as a result, security researchers agree iPhone is the safest, most secure consumer mobile device on the market,” he said in a statement.

“Attacks like the ones described are highly sophisticated, cost millions of dollars to develop, often have a short shelf life, and are used to target specific individuals. While that means they are not a threat to the overwhelming majority of our users, we continue to work tirelessly to defend all our customers, and we are constantly adding new protections for their devices and data.”
Other IT professionals, however, have been far more commending. Security researcher Bill Marczak, a fellow at Citizen Lab, a research institute based at the University of Toronto’s Munk School of Global Affairs & Public Policy, said: “Your iPhone, and a billion other Apple devices out-of-the-box, automatically run famously insecure software to preview iMessages, whether you trust the sender or not. Any Computer Security 101 student could spot the flaw here.”
What is iMazing?
iMazing released its spyware detection tool, detecting NSO’s Pegasus and other spyware on iPhone and iPad. The methodology implemented by iMazing closely resembles the open-source Mobile Verification Kit by Amnesty International’s Security Lab. It does this by searching for known malicious file names, links, processes and emails.
iMazing’s guide on using iMazing spyware detection:
- Launch iMazing on your Mac or PC and connect your iPhone or iPad via USB.
- Unlock your device and enter your passcode to establish a pairing with the computer.
- In the Actions panel, scroll down and click Detect Spyware.
- Follow the information and configuration steps carefully.
- Read the analysis report and refer to the documentation for help.
READ MORE:
- Prevention is better than cure: the ransomware evolution
- Proofpoint: why email is the top cybersecurity threat in 2021
- SolarWinds IT Trends Report 2021: Building a Secure Future
- Snow Software on cybersecurity trends and challenges in 2021
Though iMazing cannot prevent spyware like Pegasus, it is an important advancement for individuals to identify if their device has been compromised. While Apple’s cybersecurity credibility comes increasingly under question, we can remain confident that Apple and other third-party developers will continue to develop solutions to mitigate against these evolving threats.
For more news from Top Business Tech, don’t forget to subscribe to our daily bulletin
-

TPIs are the Future of Energy Solutions
-

Quick Commerce and the Retail Media Revolution
-

How Construction Companies Can Leverage Cloud Bursting
-

Is It Time for a VMware Alternative?
-

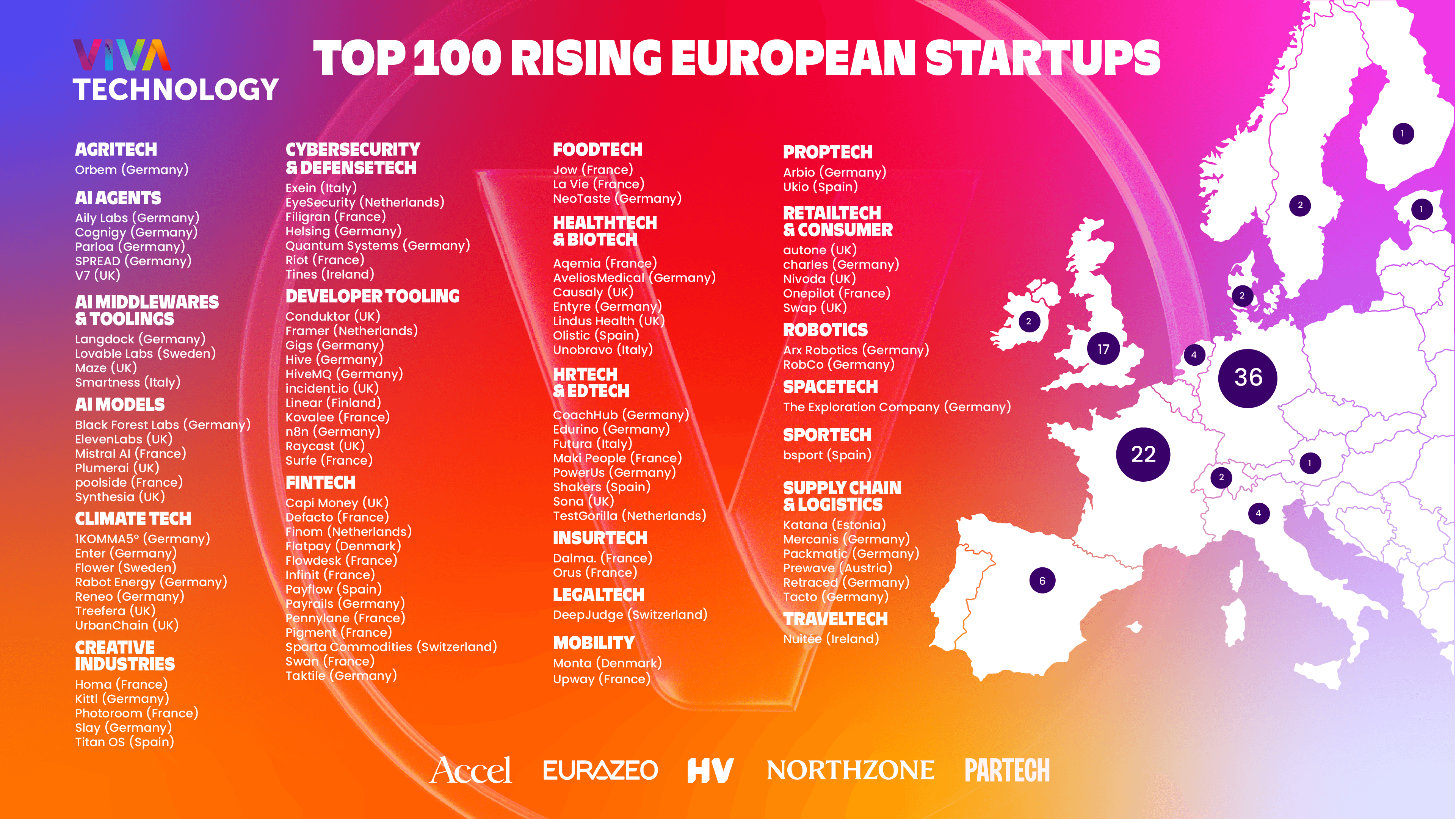
AI Leads as VivaTech Unveils Top 100 Startups
-

Birmingham Unveils the UK’s Best Emerging HealthTech Advances