How does face recognition software work?
Credit: Medical News Today
Face recognition software uses deep learning algorithms to compare a face to another. The possibilities of the technology are both concerning and extraordinary.
Face recognition software is one of machine learning’s crowning glories. It can be used to unlock your phone or hunt criminals and it’s still in its infancy.
However, like much of artificial intelligence, face recognition isn’t widely understood by the general population. It probably would come as quite a surprise to a lot of Facebook users if you told them that AI is helping to tag their friends in photos on the site. Have the machines silently infiltrated us without telling us?
The technology isn’t as insidious as the conspiracists may suggest. Facial recognition software is still a fantastic introduction to machine learning though, using relatively simple algorithms, especially compared to much of what artificial intelligence is capable of.
In order to understand face recognition, it’s important to understand how machine learning works as a whole.
The basics of machine learning and facial recognition
Technology revolves around data. Even at the most basic level, you put numbers into a calculator, ask it to complete a simple addition and receive a result in return.

Machine learning provides answers without you asking a specific question. Rather than writing code to return a result – for example, 2+2 – you feed data to an algorithm which builds its own logic based on the data.
So when it comes to face recognition software, an algorithm finds uses the data that it has to find features of a face. It then compares those features against other data it has on faces to find a similar match.
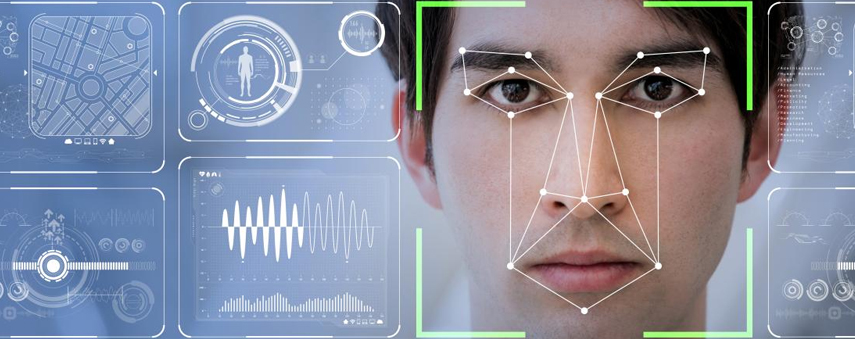
Facial recognition software does this by building a pipeline. This is basically a template explaining to the computer where the facial features are. First, an algorithm finds a face by detecting the brightness changes in a photo – the whites of eyes and teeth are giveaways of where a face is, for example – before another algorithm splits the face up into 68 separate points. Think of these as dot-to-dot style landmarks charting the eyebrows, eyes, nose, lips and outline of the face.
This points combine to create a pipeline. The outline of a face will remain fairly constant, whatever direction the subject is looking and whatever the conditions of the picture.
How does face recognition software tell one face from another?
Imagine you’re being asked to find someone from a group of people. The best way to do this is to have a photo of them to hand so that you can compare the person you’re trying to find with the same person in your photo.
The way that facial recognition software works is similar. A Convolutional Neural Network (CNN) generates 128 measurements for the face, from the shape of the nose to the length of the eyebrows, generating a picture of what that particular face looks like.
Machine learning provides answers without you asking a specific question. You feed data to an algorithm which builds its own logic based on the data.
An algorithm needs to compare these measurements across other pictures. It compares the faces of another person with the two pictures of the person it knows it’s looking for. It repeats this across countless images of different people: the CNN then learns to generate 128 measurements for every person.
Once a CNN has been trained to recognise a face, it can generate measurements for anyone. When you unlock your phone with facial recognition, an algorithm generates measurements for the face that it’s currently seeing and compares it against the face that it has on record. Biometric recognition works in a similar way, taking your fingerprints instead of a face; iris recognition is similar too.
Finally, using a basic machine learning classification algorithm will assign a name to a face: something that many of us could do with at events and parties.
What is the future of face recognition software?
In Qingdao, China, 25 people were arrested after arriving at a beer festival. One of those apprehended had been on the run for ten years.
The festival employed a facial recognition system at its gates. Authorities boasted of the system’s accuracy being over 98% and the episode raised a number of questions about how facial recognition could be used not just by the police but private establishments. With the advent of China’s social credit system, it’s a relevant discussion.
Face recognition software could be used to refuse entry to anyone on a blacklist. Whether that’s used for underage individuals restricted from visiting nightclubs or football hooligans banned from stadiums, the technology could be installed at virtually any gate. It’s already in use at gyms and workplaces.

Perhaps the most exciting implementation of the software would be to use it as a kind of ID card, though. What if technology accelerates to the point where drivers can be facially scanned if they’re pulled over by police officers? What if we could buy items from shops simply by looking into a scanner? Could we crack down on revenge porn, catfishing and fraud if you were notified when a photo of you is uploaded, wherever it was uploaded?
The possibilities are huge and the technology is relatively straightforward. Face recognition software is still in its early stages but it’s one of machine learning’s most impressive feats and it will only get more advanced with time.
